20 Free Tips For Picking A Zk-Snarks Privacy Website
Wiki Article
The Zk Shield That Powers It: What Zk Snarks Protect Your Ip And Identification From The World
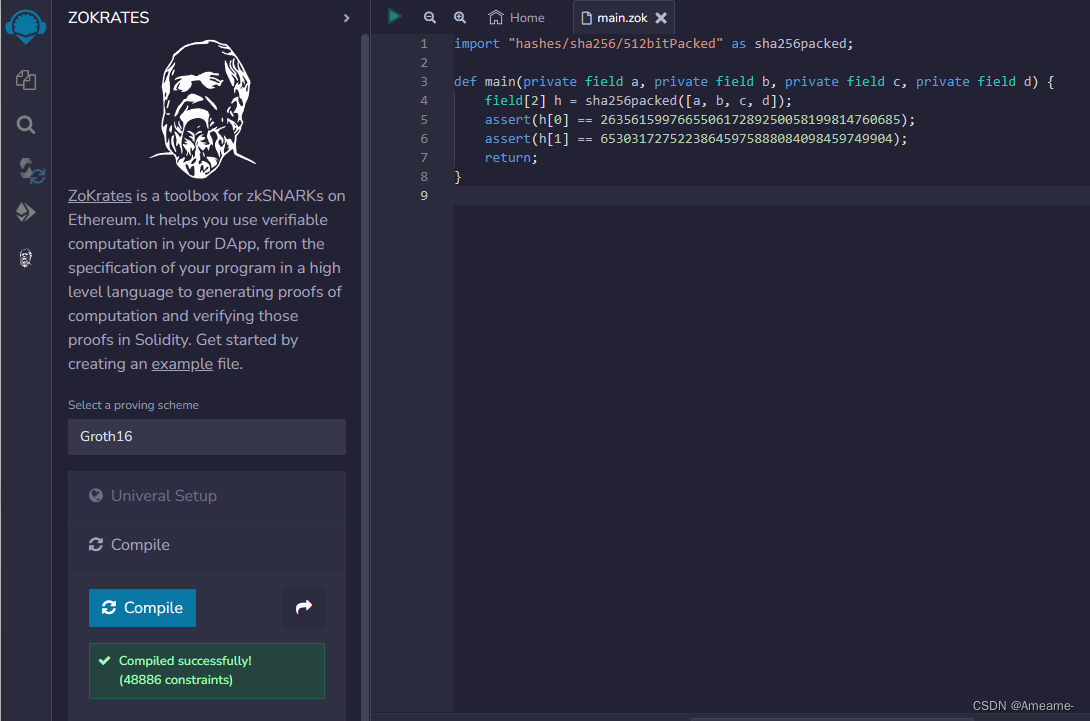
For a long time, privacy-related tools operate on the basis of "hiding from the eyes of others." VPNs connect you to another server, and Tor can bounce you between some nodes. The latter are very effective, but they are essentially obfuscation--they hide that source by moving it away, and not by convincing you that it doesn't need to be revealed. zk-SNARKs (Zero-Knowledge Succinct, Non-Interactive Arguments of Knowledge) introduce a distinct paradigm that must prove you're authorized to perform an action with no need to disclose who the entity is. In Z-Text, this means you can broadcast a message that is sent to BitcoinZ blockchain, and the network will verify that you're a legitimate participant with a valid shielded address, but cannot identify the particular address was the one that sent the message. Your address, your name, your existence in the discussion becomes mathematically unknown to the viewer, but verified by the protocol.
1. The dissolution of the Sender-Recipient Link
Traditional messaging, even with encryption, discloses the communication. Someone who observes the conversation can determine "Alice has been talking to Bob." Zk-SNARKs cause this to break completely. In the event that Z-Text transmits a shielded zk-SNARK an zk proof confirms the transaction is legitimate--that is, that the sender is in good financial condition as well as the appropriate keys. It does not reveal addresses of the sender and the recipient's address. For an outsider, the transaction can be seen as sound wave that originates that originates from the entire network and not from any specific participant. The connection between two humans becomes computationally unattainable to confirm.
2. IP Privacy Protection for IP Addresses at Protocol level, not the Application Level.
VPNs as well as Tor protect your IP by routing your traffic through intermediaries. However, the intermediaries will become a new source of trust. Z-Text's use with zk-SNARKs implies that your personal information is not crucial to verifying transactions. When you transmit your private message through the BitcoinZ peer-tos-peer network, you belong to a large number of nodes. The ZK-proof makes sure that observers observe the network traffic, they cannot link the messages received with the wallet which originated it, because the verification doesn't provide that data. The IP's information is irrelevant.
3. The Elimination of the "Viewing Key" Conundrum
For many privacy and blockchain systems it is possible to have"viewing keys" or "viewing key" that allows you to decrypt transaction information. Zk-SNARKs, which are part of Zcash's Sapling protocol which is employed by Ztext can be used to allow selective disclosure. You can prove to someone that you've sent a message without revealing your IP, any other transactions or even the entirety of the message. The evidence is the only evidence being shared. A granular control of this kind is impossible with IP-based systems, where the disclosure of an IP address will expose the sources of the.
4. Mathematical Anonymity Sets That Scale Globally
If you use a mixing service, or VPN Your anonymity is restrained to only the other people with that specific pool the exact moment. With zkSARKs you can have your privacy will be guaranteed by every shielded address on the entire BitcoinZ blockchain. Because the confirmation proves the sender's address is protected address, which could be million, but does not provide any hint which one, your privacy scales with the entire network. Your identity is not hidden in only a few peers at all, but within an entire number of cryptographic identities.
5. Resistance to attacks on traffic Analysis and Timing Attacks
Highly sophisticated adversaries don't simply read IP addresses, they also analyze patterns of traffic. They determine who's transmitting data when, and correlate timing. Z-Text's use in zkSNARKs as well as a blockchain mempool permits decoupling an action from broadcast. It's possible to construct a blockchain proof offline before broadcasting it as a node will broadcast the proof. The time of proof's being included in a block is undoubtedly not correlated with day you built it, defying timing analysis which frequently beats more basic anonymity tools.
6. Quantum Resistance With Hidden Keys
It is not a quantum security feature; if an adversary can track your online activity now in the future and then crack your encryption, they can link them to you. Zk-SNARKs(as used in Ztext, protect your keys by themselves. Your private key isn't disclosed on blockchains because it is proof that proves you've got the right key without actually showing it. Even a quantum computer in the near future, will examine only the proof but not your key. All your communications are private due to the fact that the code used to be used to sign them was never revealed as a hacker.
7. Unlinkable identities across several conversations
By using a single seed for your wallet it is possible to generate several protected addresses. Zk SNARKs will allow you to prove to be the owner address without having to reveal which one. The result is that you'll have 10 conversations with ten different people, and no witness, even the blockchain cannot track those conversations through the one and the same seed of your wallet. The social graph of your network is mathematically broken up by design.
8. Removal of Metadata as a security feature
Regulators and spies often say "we aren't requiring the content or the metadata." IP addresses are metadata. What you communicate with is metadata. Zk-SNARKs differ from other security technologies due to their ability to hide metadata in the cryptographic realm. The transactions themselves do not have "from" or "to" fields that are plaintext. There's no metadata attached to request. Only the proof, and the proof can only prove that a legal act took place, not the parties.
9. Trustless Broadcasting Through the P2P Network
When you sign up for a VPN, you trust the VPN provider to not record your. While using Tor, you trust the exit network not to spy. With Z-Text you send transactions that are zk-proofed to the BitcoinZ peer-to-peer networks. You connect to a few random networks, share the data, then switch off. Nodes can learn nothing since the data does not prove anything. It is impossible to know for sure that you're actually the creator, since you may be acting on behalf of someone else. This network is a dependable storage of your personal data.
10. "The Philosophical Leap: Privacy Without Obfuscation
Additionally, zk's SNARKs mark some kind of philosophical leap, in the direction of "hiding" towards "proving by not divulging." Obfuscation techniques recognize that the truth (your ID, IP) can be risky and needs to be concealed. ZkSARKs are able to accept that the reality cannot be trusted. A protocol must only know that you are certified. The change from reactive disguise to active irrelevance forms what powers the ZK protection. Your identity and your IP are not obscured; they are essential to the nature of a network and thus are not required as a result of transmission, disclosure, or even request. Have a look at the most popular wallet for more advice including messages messaging, phone text, instant messaging app, messages messaging, encrypted message, messenger not showing messages, encrypted text app, private text message, messenger to download, messenger with phone number and more.
Quantum-Proofing Chats: What's The Reason? Z-Addresses As Well As Zk-Proofs Defy Future Cryptography
Quantum computing can be described as a boogeyman for the future which will destroy encryption completely. However, the truth is much more intricate and urgent. Shor's program, if used with a sufficient quantum computer, might theoretically break the elliptic of curve cryptography, which safeguards a large portion of the internet and bitcoin today. However, not all cryptographic methods are the same. Z-Text's system, based on Zcash's Sapling protocol as well zk's SNARKs includes inherent properties that prevent quantum encryption in ways traditional encryption methods cannot. The main issue is what is public and what's kept secret. In ensuring that your private details aren't disclosed to Blockchain, Z-Text protects you from nothing for a quantum computer to exploit. Past conversations, your identities, and the wallet remain safe, not through any other factor, but instead by its mathematical invisibility.
1. A Fundamental Security Risk: Exposed Public Keys
To better understand the reason Z-Text's technology is quantum-resistant is to first know why many systems are not. With standard blockchain transactions the public key of your account is disclosed every time you invest funds. A quantum computer is able to take the publicly exposed key and through Shor's algorithm create your private key. Z-Text's shielded transaction, using an address called z-addresses don't reveal an open public key. The zkSARK is evidence that you've access to the key without revealing. The public key is concealed, giving the quantum computer nothing to attack.
2. Zero-Knowledge Proofs in Information Minimalism
zk-SNARKs are inherently quantum-resistant because they use the difficulty of problems that can't be much solvable by algorithmic quantum techniques like factoring or discrete logarithms. But more importantly, the proof itself reveals zero details on the witness (your private secret key). While a quantum-computer might theoretically defy the basis of the proof, it's not going to have anything to play with. It's simply a digital dead-end that validates a declaration without including what it is that the statement's content.
3. Shielded Addresses (z-addresses) as being obfuscated existence
A z-address within the Zcash protocol (used by Z-Text) is never published by the blockchain system in a way where it can be linked to transaction. If you get funds or messages, the blockchain only notes that a shielded-pool transaction happened. Your personal address is hidden inside the merkle tree of notes. A quantum computer scanning the blockchain only detects trees and proofs, not leaves and keys. Your digital address is encrypted but isn't visible, making your address unreadable for analysis in the future.
4. Defense: The "Harvest Now, decrypt Later" Defense
The biggest quantum threat of today isn't an active attack however, but a passive collection. Intruders are able to scrape encrypted information from the web and store it until quantum computers to get better. With Z-Text one, an adversary has the ability to get into the blockchain and capture all shielded transactions. If they don't have the keys to view and never having access to the public keys, they will have no way to crack the encryption. Data they extract is unknowledgeable proofs designed to will not have encrypted messages which they would later crack. The message cannot be encrypted inside the proof. Instead, the proof is the message.
5. The significance of using a single-time key of Keys
In many cryptographic system, reusing a key creates more vulnerable data for analysis. Z-Text, built on the BitcoinZ blockchain's application of Sapling permits the using of diverse addresses. Each transaction has an entirely unique, non-linked address stemming from the identical seed. That means, even there is a chance that one address could be damaged (by any other method that is not quantum) all the rest are protected. Quantum resistance gets a boost from an ongoing rotation of key keys which limits the value of just one broken key.
6. Post-Quantum assumptions in zkSARKs
Modern zk-SNARKs rely heavily on an elliptic curve pair, which are theoretically susceptible to quantum computer. However, Z-Text's specific structure employed in Zcash as well as Z-Text can easily be converted to a migration-ready. The protocol was created to enable post-quantum secure zk-SNARKs. Because keys aren't released, a change to completely new proving technology can be achieved through the protocol, not being obliged to make public their background. Shielded pools are capable of being forward-compatible with quantum resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet seed (the 24 words) doesn't have to be quantum-secure in the same manner. Seeds are essentially large random number. Quantum computers don't do much superior at brute-forcing random 256-bit numbers than conventional computers due to the limits of Grover's algorithm. The vulnerability is in the process of obtaining public keys from that seed. Through keeping these keys under wraps with zk SARKs, that seed remains secure even after quantum physics.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
Although quantum computers may make it impossible to use encryption for certain aspects But they're still facing an issue with ZText obscuring metadata within the protocol. If a quantum machine is able to reveal that a certain transaction that occurred between two participants if they were able to reveal their keys. In the event that those keys aren't revealed as well as the transaction is only a zero-knowledge evidence that doesn't include addressing information, this quantum computer has only that "something took place within the shielded pool." The social graph, timing also remain in the shadows.
9. Merkle Tree as a Time Capsule. Merkle Tree as a Time Capsule
Z-Text is a storage system for messages within the blockchain's merkle trees of encrypted notes. This type of structure is inherently impervious to quantum decryption as the only way to discover a particular note you need to be aware of the note's commitment to the note and where it is within the tree. Without the key to view, quantum computers cannot differentiate your note from millions of notes that are in the tree. The time and effort needed to searching the entire tree for an exact note is exorbitantly heavy, even on quantum computers. This effort increases with each block added.
10. Future-proofing by Cryptographic Agility
The most crucial feature of Z-Text's quantum resistivity is its agility in cryptography. Since the technology is built using a blockchain protocol (BitcoinZ) which is developed through consensus by the community Cryptographic techniques can be replaced as quantum threats materialize. Customers aren't bound by one algorithm for the rest of their lives. Additionally, as their history is shielded and their keys are self-custodians, they are able to migrate into quantum-resistant new curves, without having to reveal their previous. The technology ensures that conversations are safe not only against threats of today, however against those of the future as well.